Intelligence or Investigations reports are important for the success of an investigation. But how do you make sure that they are written in a way that makes sense for anyone who needs to read it, regardless of technical background?
We have spoken to Dario Beniamini, CEO and owner of Intellexia, about best practices for writing digital forensics reports.

Telling a story in a digital forensics report
Information in an investigation can be extremely technical and difficult to validate. In the report the information should be explained in a way which is accessible for everyone.
– In my opinion, the goal of the report is to tell a story, says Dario.
Telling a story in a report is like writing an article or a book. You need to make sense of the story, connect all the pieces together and write it in a way that everyone can understand and follow.
– If you have a nice idea about a book, but your story doesn´t make sense when written down, the reader will just close the book. The same applies for a report. If we just provide what we collected without analysing and making sense of the story, we are not investigators, we are only collectors of evidence, says Dario.
A report could be used in different ways by people with different kinds of backgrounds. It might for example be escalated to the CEO of an insurance company. And if they don’t have a technical background, which they usually don’t , they might not understand a far too technical report.
In other words, simplification is the key to a good report.
So are you saying that I should not include technical data in my report?
Of course you should. Telling a story that anyone can understand is really important. But it is also important to include things like hash values, time stamps, assets, OSINT data, ip addresses and more.
You need all this information to make the evidence legal from a forensics point of view. But all this is something which could be included in the appendix since it is not important for the actual story.
– A CEO for example doesn’t want to read all that. They expect that if you present them with evidence, you have already done everything needed to make it legally valid, says Dario.

Writing guidelines for a digital forensic report: What should be included and how should it be structured?
This is not a simple question. What should be included in the report depends on what kind of investigation you are working on.
– The purpose of the report can vary. Myself for example work in different fields, like open source intelligence, brand protection investigation and digital forensics investigations. Every type of activity has different report structures and types of information that should be included in the report, says Dario.
So, it is not possible to give a one-solutions-fits-all structure.
But here is an example of a structure which Dario follows when working with OSINT investigations.
The first four steps are where you are telling the story. These should be written on a maximum of 2 pages and easy for the reader to understand.
- Scope including: requested by/provided by/date of receipt/type of activity.
- Executive Summary: A summary of the activities completed including a brief analysis and an image that gives you an overview of the investigation. Like a map, a link chart or an image of the investigated entity. An executive summary should not be longer than one page.
- Proposed Next Steps: 3 or 4 sentences based on what was found in the investigation, give examples on things to do next. It could be something like filing a criminal complaint.
- The investigation itself, meaning the story behind the investigation and how the evidence was identified and validated. In this part the evidence needs to be related to the story so the reader is able to understand why that information was reported and documented.
Here is an example on how this first part could be written. This is of course a fake investigation since we can´t share a real one.
Scope
- Date (receipt): 01.06.2021
- Provided by: Ray KROC
- Provided via: email on May 30th, 2021
- Investigation Task: Asset tracing of PERSONS (focus on real estate in Rome, Italy)
The investigation is focused on asset tracing, with a particular attention to real estate properties about the following two Italian citizens:
- Mr. Mario ROSSI
- Ms. Anna VERDI
Executive Summary
The scope of the investigation was to identify real estate properties connected to the above- listed subjects of investigation. Mr. Mario ROSSI is the only subject who has several properties near Rome (RM).
All subjects are linked through Facebook friendships, and they all belong to the committee “Pizza Forever”. Mr. ROSSI has political experience as councilman of the Municipality of Rome (RM) with the party MOVIMENTO PIZZA 4ALL (MP4A) and a respectable curriculum vitae as a “pizzaiolo” in Italy, USA, and Japan.
All subjects seem to have sympathy for the slow food cause and to the pizza party. They also joined other committees against the Chicago Pizza and new fast foods franchise in Rome. Ms VERDI and Mr. ROSSI seems to have brought a civil action against MacPizza for damaging the image of the Roman Pizza in Chicago.
Proposed Next Steps
It is suggested to have a local P.I. to conduct a HUMINT investigation to better understand the connections between the Subjects of the investigation, the party MOVIMENTO PIZZA 4ALL (MP4A), the Italian food association named “Pizza Forever”, and other committees such as “No MAC Pizza”, “No Burger Pizza”, “No Pizza No Party”, etc.
Investigation
The data collected during the investigation was identified on Italian Public Registries (such as the Cadastral Registry or the Civil Registry), private Italian databases, with primary research completed by a local P.I. over the phone and secondary research using OSINT techniques on open (such as Search Engines and online Newspaper) and deep web (such as Social Networks) resources.
The next 9 parts are a bit more technical. These parts are also important to validate your story written on the first two pages.
1.Investigated person/company data (data identified on public registries)
A summary table which includes data used to identify the person or the company. The information to include here are:
- Person: First and last name, Alias name, Marital status, Date and place of birth, Nationality, IDs, Photo, Address, Residency, Phone number(s), email(s),
- Company: Company Name, VAT number, Registered Office, Secondary address(s), Telephone number(s), Fax number(s), Certified Email, Secondary Email(s), Website(s), Company Type, Date of Establishment, Company Registration #, Date of Registration, Administrator(s), Board of Auditor (BOA), Shareholder(s), Share(s) / Participation(s).
2. Financial Information
Data identified on private registries if available. Bank Account(s) Registered, Bankruptcy / Seizure(s) / Legal Action(s)
3. Assets
Data identified on private registries if available. Real Estate properties, vehicles, boats, etc.
4. Employment
Data identified on private registries if available and/or Social Networks (LinkedIn, Xing, Facebook, etc.)
5. OSINT Data
Every piece of validated intelligence identified via OSINT techniques on open/deep, such as Social Networks or proprietary databases, etc.
6. OSINT Map
Every piece of validated intelligence identified via OSINT techniques and georeferenced
7. Media Research
Data identified on local newspaper or databases which aggregate local newspapers that do not have an electronic version
8. HUMINT
Data identified via Human Intelligence such as results of an investigation from a private investigator, surveillance, a source of confidential information, etc.
9. Due Diligence/OSINT analysis
The analysis of all evidence reported in step 1-8
And then for the last part of the report Darios adds:
- Relationship graph (Link Analysis & Timelines)
- Appendix
- Research sources
- Files
- Collected Data

What should be avoided when writing a digital forensic report?
One thing that should be avoided is including too much information not related to the investigation. If the report is too long with irrelevant facts, no one will read it. The same applies if the report is too technical.
– We need to understand the final recipient of the report. I am not a writer myself. I have a structure which helps me to focus on important information. So when I write a report, I already know what is important to include, and what’s not, says Dario.
Don’t do anything illegal when collecting evidence
When writing a report it is important to do it in an objective way.
– At the end of the day, you are not a judge and a report is not a place for opinions, especially when related to digital forensics investigation or data collected on the open web. Your report should be based on experience, access, legal activities and stated facts, says Dario.
When it comes to legal activities it can vary depending on which organisations you work for or what country you are in.
In some jurisdictions it is a crime to do pretexting or to create a sockpuppet to interact with someone on the Social Network. Only a law enforcement agency should create sockpuppet when authorized by a public prosecutor
One thing is to observe, another thing is to interact and that is something you should always have in mind when collecting evidence.
– You need to do everything in a legal way. If your report is to be used in court, and you have collected it in an illegal way, you could jeopardize the entire investigation and potentially go to jail, says Dario.
This even applies to law enforcement.
– Not even law enforcement is above the law. If they contact someone in an illegal way, they could for example be accused of being provocators. And if something bad happens because of their actions, they can be prosecuted and evidence can be removed because they were acquired illegally, even if they are the law enforcement themselves, says Dario.
So in order to not make any mistakes, make sure you know what’s legal and what’s not in the country you are operating in.
3 tips for making the report process more effective
To wrap this up we asked Dario to give us his three best tips to make reports more efficient.
This is what he told us.
- Take structured notes of your findings as your investigation progresses. This makes it easy to just copy and paste information into the final report.
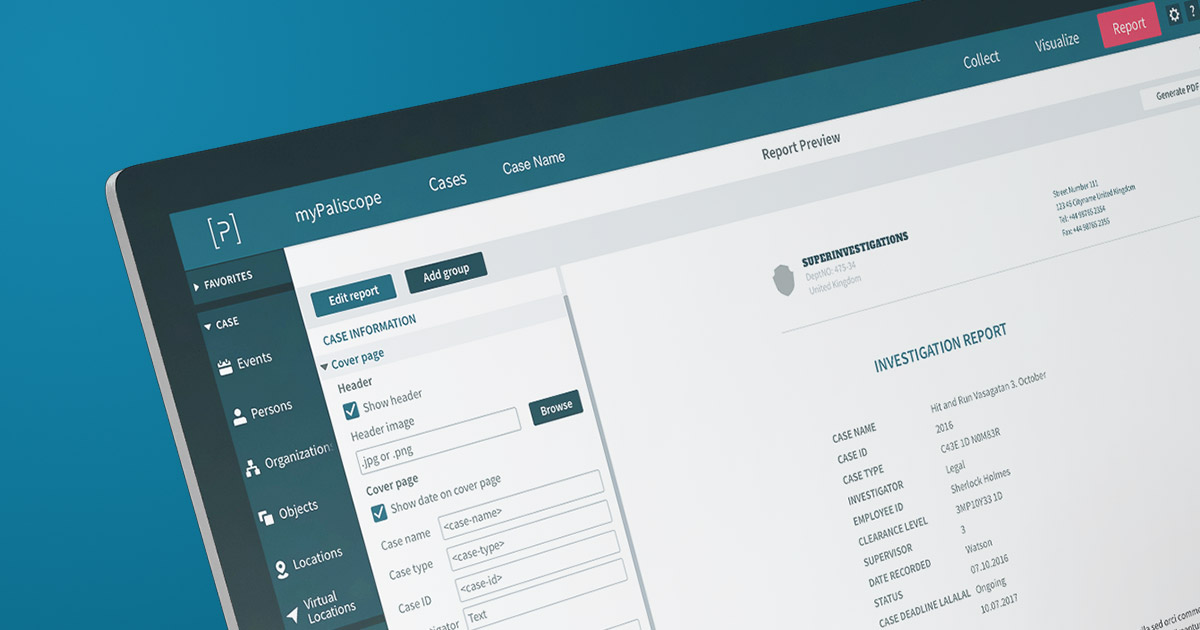
- Using a tool such as Discovry helps in taking notes, preserving evidence and conducting audit trails while you are performing an investigation. If not using Discovry it means doing all this manually. Manually means losing time, which ultimately means losing money and for me this is a waste. Using dedicated tools helps a lot.
- Simplification is key. Do not make things more complex than they are. You don’t know who the final recipient is and if you make things too complex or technical, they might not be able to understand the report.
We hope that you found this article useful.
Get in touch!
Reach out to learn more or discuss how we can help you in your work.





