Modern law enforcement investigations often deal with vast amounts of digital data. In this digital age, suspects leave traces across various platforms and mediums, creating a “digital footprint.”
Digital profiles consolidate this fragmented data into coherent, actionable insights. By systematically organizing and analyzing these profiles, investigators can uncover connections, monitor activities, and respond more effectively to criminal activity.

Modern law enforcement investigations often deal with vast amounts of digital data. In this digital age, suspects leave traces across various platforms and mediums, creating a “digital footprint.”
Digital profiles consolidate this fragmented data into coherent, actionable insights. By systematically organizing and analyzing these profiles, investigators can uncover connections, monitor activities, and respond more effectively to criminal activity.
A digital profile is a structured representation of an individual’s online and offline activities, characteristics, and connections. These profiles are invaluable for understanding suspects or persons of interest in investigations.
Key elements of a digital profile include:
Name: Official names or pseudonyms from identification documents or online accounts.
Usernames: Handles used on platforms like social media, forums, or messaging apps.
Media: Photos, videos, voice recordings, or other multimedia content linked to an individual.
Locations: Geographical data derived from posts, metadata, or surveillance systems.
Account numbers: Bank accounts, cryptocurrency wallets, or similar identifiers.
Alias avatars: Profile pictures or digital representations used in online spaces.
Other data: Communication patterns, timestamps, or connections across multiple platforms.
By compiling these data points, investigators gain a comprehensive view of a person’s digital and physical presence.
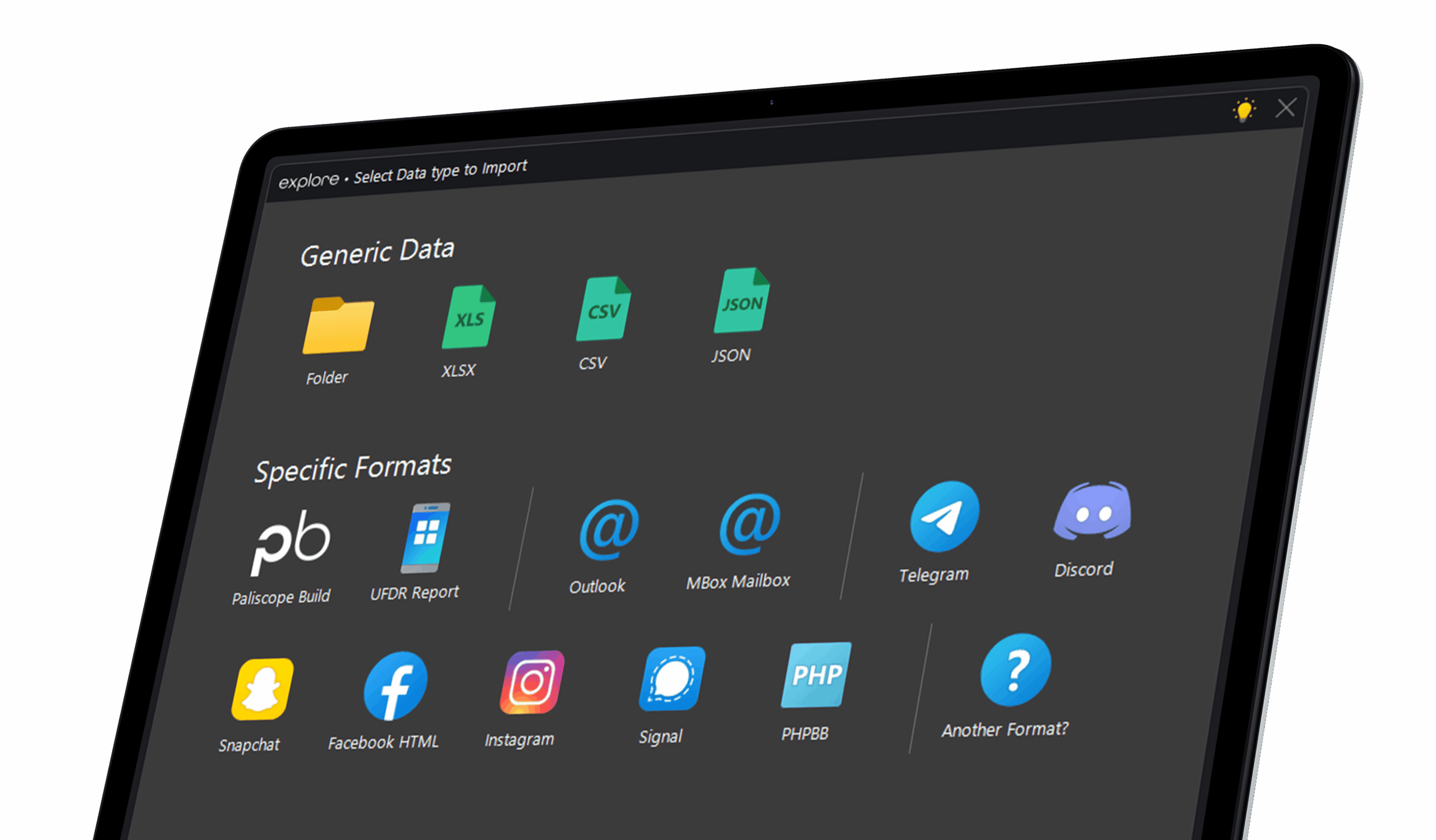
Digital profiles are built from a variety of data sources. Each type provides unique insights. Here are a few examples:
Scraped data: Extracted from social media, forums, or websites. This can include public posts, comments, or activity logs.
Mobile phone extractions: Accessing messages, photos, call logs, and app data from seized devices.
CCTV footage: Identifying movement patterns, facial recognition, or object tracking.
Cell tower dumps: Analyzing connections between mobile devices in a specific location and timeframe.
CSV files and databases: Structured data from investigative systems or external sources like financial institutions.
Combining these sources creates a multidimensional view of the subject, enabling deeper analysis.
Both technical and human monitoring have essential roles in modern investigations:
Technical monitoring: Leverages technology to scan massive datasets for patterns, anomalies, or predefined triggers. Example: Detecting a known alias in a database of millions of messages.
Human monitoring: Provides context and critical thinking, interpreting the significance of technical findings. Example: Understanding the cultural or contextual meaning behind flagged keywords.
A hybrid approach ensures accuracy and maximizes the strengths of both methodologies.
Using analytical software tools like Paliscope Explore will enable investigators to do the heavy lifting – going through large volume data sets with speed and precision. With Paliscope Explore it is possible to search with text, images, faces, visually similar, and other artifacts such as metadata – enabling investigators to find what they are looking for with a click of a button. Adding technical monitoring like alerts and automated keyword searches on new data makes it possible to find all things related to a digital profile even in large, growing datasets.
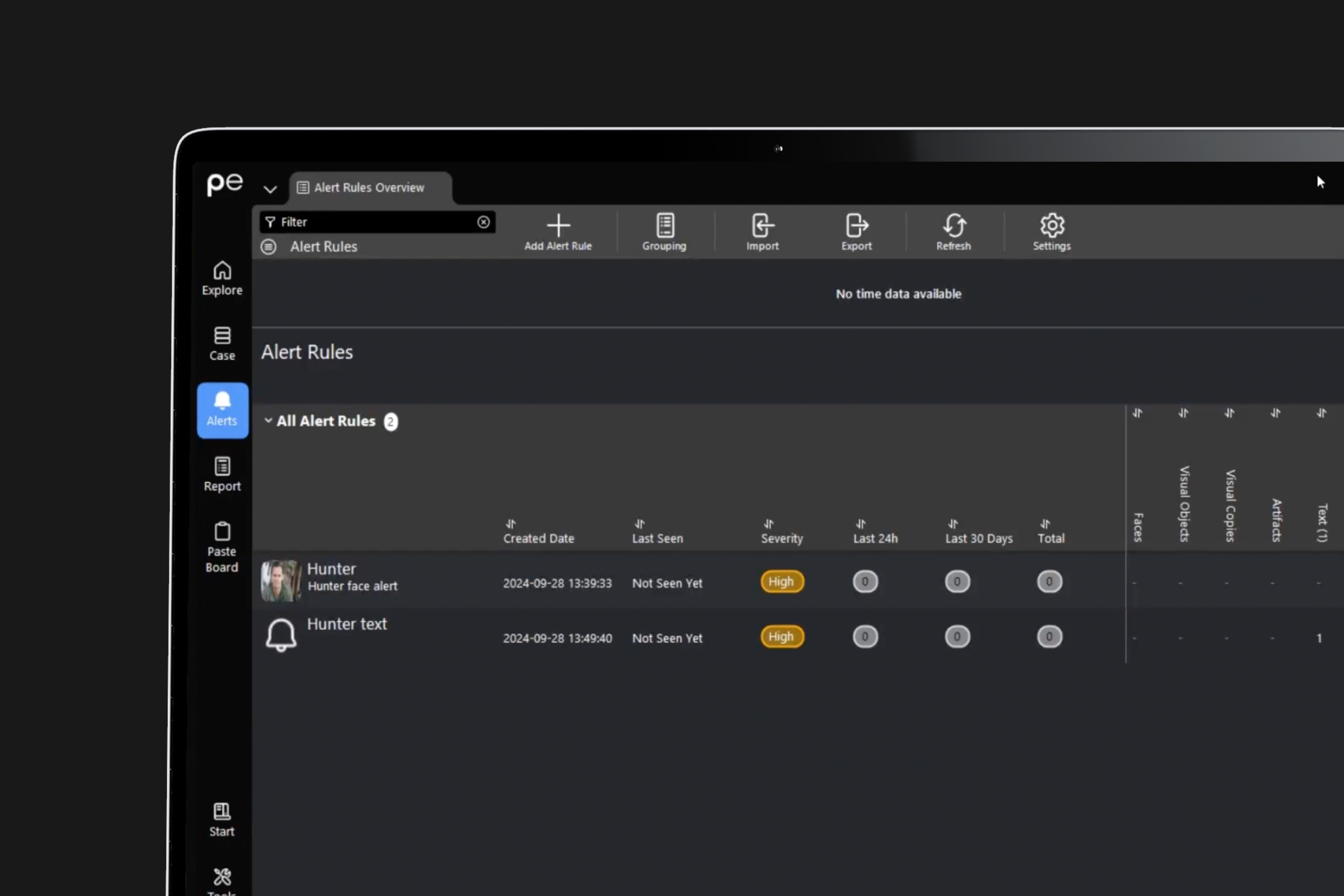
Technical automation can significantly enhance investigative efficiency:
Alerts for media and text:
Keyword search strategies:
Automation ensures investigators are immediately informed of relevant updates, reducing manual monitoring.
Effective data organization is essential for managing complex investigations. Structuring your data through both static and active folders ensures you stay organized while keeping up with the constant flow of new information.
Static folders: Use static folders to store relevant data, such as evidence from specific sources, profiles, or chronological timelines. These provide a structured, reliable way to organize and access data as needed.
Active folders: Active folders are ideal for handling continuous streams of incoming data. These dynamic folders automatically import new files as they appear, saving you time and ensuring your analysis stays up to date.
For instance, you can set up an active folder to collect scraped data, which can then be seamlessly uploaded to Paliscope Explore. This allows you to monitor emerging trends, identify connections, and stay ahead in real time.
By leveraging both static and active folders, you can reduce administrative tasks and focus on what matters most.
Consider a case where an investigator uses digital profiling to track a suspect in a financial fraud case:
Initial data collection: Scraping social media accounts reveals aliases and linked usernames.
Alerts and monitoring: Set up alerts to get notified when data containing the suspect’s username and/or chosen keywords like “Bitcoin” or “transfer” appear.
Active folders: Direct all scraped data to an active folder and automatically upload all incoming data to Paliscope Explore.
Cross-platform analysis: Combine data from CCTV, phone extractions and other sources to e.g. correlate physical locations with online activity.
Such structured approaches accelerate case progress and provide actionable insights.

No need to worry about evidence documentation and report formatting. Paliscope Build automates all that - keeping your cases structured, secure and easy to hand over.
Find what you are looking for with Paliscope Explore - enabling analysts and investigators to triage large amounts of data and deep dive into the findings.
Process all your data in one place, collaborate across teams, search for anything, and more.