If you are working with digital forensics, this article is for you. Doing digital forensics is one of the most important jobs you can have. The investigator gathers all the evidence needed to lock criminals away. Heroes in our eyes!
But it is not an easy job. There is so much that can go wrong while investigating, and when it does — criminals can get away.
In this article, we are sharing best practices for digital forensics. What steps to take. Do’s and Don’ts. What tools to use and what certifications and skills needed to do a great job.
We go through:
- Six steps of digital web forensics
- Which tools to use for a digital forensics investigation
- Important skills
- Courses and certifications
- The importance of keeping yourself updated
- Legal aspects
Skip to the part you want to read more about or take time to read it all. This article will give you all the knowledge you need to become a great digital forensics investigator.
The many sub-disciplines of the digital forensics Process
Digital forensics is broad with many sub-disciplines. It includes computer forensics, mobile forensics, network forensics, and web forensics.
In many ways, the process is similar and requires the same tools. But there are some differences in where you look for evidence and how you secure them. In this article, we will take you through the process of web forensics since that’s something we work with a lot at Paliscope.
Every country has its own laws, and what respective law enforcement agencies are compelled to do varies a lot. Therefore it is difficult to lay out a sequential series of steps for the process.
But there are some general procedures that everyone does no matter what country you´re working from. These are important to follow since a case can be discarded if not appropriately handled.
Let’s take you through the steps.

Step 1 — Securing the working environment.
Having a secure environment is crucial for the case you are investigating. If there is any gap where you can´t show that the evidence was securely stored, a defense legal team will find it and use it against your case.
So how do you secure your working environment?
There are some essential things you need to do, which are:
- Have a sign-in, sign-out process.
- Make sure you have the right tools.
- Use a computer for only the purpose of investigations (no private use)
- Use a Sock Puppet when investigating.
Leave no fingerprints behind.
For your own safety and your organization, it is crucial to know how to investigate online without leaving digital fingerprints. You don’t want anyone to discover you since it can severely complicate the investigation even further.
Here are some safety aspects to consider when investigating:
How cookies works
A cookie is a more friendly term to describe a tracker – but in reality, its function is to track user behavior.
Whilst most cookies are harmless, some can be used to gather information about you. At the same time, some online services are known to use cookies to create a profile about you and your online behavior.
Each time you visit a website, that website may store a cookie on your computer – via the browser. Then, when you revisit the same website, your browser sends the information back to the site.
The problem with cookies is that there is a potential risk of being discovered by criminals. Cookies can give away the fact that you are investigating something which could interfere with your investigation.
So how do you keep cookies from contaminating your investigation?
Block cookies in your browser
One solution is to block all cookies from your browser. You do this by going to settings in your browser, finding preferences for cookies, and checking the “Block all cookies” box.
The problem with this solution is that many websites rely on first-party cookies to provide basic functionality. By blocking all cookies, you may find that you can’t use many important websites at all, or they will have reduced functionality.
Use investigation software
Another solution is using a system that is made for investigations. In Paliscope Build (previously called Discovry), for example, we keep your cases in separate cookie containers, separating the cases from each other, which means that information does not leak from one case to the other.
Use VPN to anonymize your IP address.
Lastly, a Virtual Private Network (VPN) and a Virtual Machine (VM) can also provide anonymity, ensuring that cookies stored on your system refer to an anonymized IP address.
However, as should be best practice at the end of any investigation, the browser and system must be cleared of Cookie data before the VPN is switched off.
How social media works
Social media platforms are designed to connect people. But they are also used by social media companies to track user behavior and measure user interests.
For Law Enforcement, social media is a valuable source of intelligence against criminal suspects as it allows investigators to potentially obtain information regarding a suspect’s movements and their inner circle.
However, the information obtained via social media is very much dependent on the privacy settings the suspect has implemented. As such, information that is not publicly visible cannot be obtained, though some countries have systems where warrants can be issued to social media companies to provide private user information.
Important: Use a “Sock Puppet” on social media
Investigations conducted on social media should be done through a fake social media profile – also referred to as a ‘Sock Puppet.’
However, when taking into account that social media companies collect user behavior, it is imperative to ensure that Sock Puppet activity is done through a VPN and is consistent in terms of searches and general behavior.
For example, a Sock Puppet created and accessed in Sweden and used to investigate criminals in the United Kingdom can be flagged.
READ MORE: How to build a solid fake identity for online investigations.
What browser you should use
What browser you should use very much depends on what your digital investigation needs to achieve.
For example, some Social Media Intelligence (SOCMINT) investigations require tools that may only be available on Mozilla Firefox. At the same time, certain web forensic activities require Google Chrome-based extensions. For Dark Web investigations, most activity will require the use of Tor.
We know this can be complex since many different systems and browsers exist. But don’t forget these important rules:
- Use a clean computer and software
Regardless of what system or browser you use to conduct your investigation, the most important consideration is the need to be digitally secure with a clean computer and software which has not been compromised from previous activities. - Use a dedicated computer for investigations.
It is essential to use a dedicated computer for the sole purpose of digital investigations, which means; no personal usage and no unnecessary activity. - Use anti-malware and VPN
In addition, investigators need effective anti-malware software and a trusted Virtual Private Network (VPN) solution.
In Build, you have access to two browsers. A clearnet browser is similar to the investigation browser Brave and the darknet browser Tor. These browsers are good to use for online investigations and are made for reducing your fingerprint.

Step 2 – Collecting evidence
By explaining safety in the previous step, we have more or less spoken about essential things to consider while collecting evidence.
These are six things to have in mind while collecting evidence:
- Do all the preparations from step 1
- Use a sock puppet
- Make sure there is an audit trail
- Document everything
- Use timestamps and hash values (more about that in step 3)
- There is no room for mistakes
Audit trail
While collecting evidence, it is crucial to have an audit trail. This means keeping a record of exactly where you collected the evidence, how you did it, what time you did it, and so on.
The audit trail needs to be bulletproof with no gaps that the legal defense team can use to poke a hole in your investigative work.
An audit trail can be made manually, but it takes a lot of time. Therefore, using a dedicated tool to do it automatically is highly recommended.
Our solution, Build, helps take notes, preserve evidence and conduct audit trails while you are investigating.
Contact us here to learn more about Paliscope Build or try it out for free.
Scraping data from social media
When collecting evidence, there are different tools you can use to scrape data from various social media platforms. You need to download Python to use most of the scraping tools. But even if you don´t have much experience, these tools are easy to use.
Here are some scraping tools we recommend:
We have written an article about the different tools you need to scrape data from various social media platforms and another article more specific on how to scrape data from Telegram.
Collecting evidence is all about doing it securely and not missing small details that can make all the difference in a case. Putting time stamps and hash values on every piece of evidence is crucial, and how to do that is what step three is all about.

Step 3 – Time stamps and hash values
A Hash Value is a fixed string of numbers and letters generated from a mathematical algorithm. This generated string is unique to the file being hashed.
If the file is altered in any way, the hash value changes, and the evidence is not to be trusted.
Hash files manually are time-consuming.
To “hash” files manually for every piece of evidence you find is time-consuming, and in any investigation having time for actual investigative work is valuable.
Manually hashing is also considered insecure based on the fact that evidence such as an HTML file can be saved, altered, and then hashed.
So how can you avoid manual work and still document your investigation in a safe way?
Unfortunately, there are no easy workarounds. To make this part of the job more efficient and safe, we suggest you use a system that does the work automatically.
There are multiple investigation systems out there. For example, if you use Paliscopes product Build. for collecting evidence, the system will automatically timestamp and hash all evidence. It also creates a protected audit trail making it easy to follow the chain of custody in the investigation.
Not only does this allow investigators to save time and use that time to develop further lines of investigation, but it also guarantees that evidence cannot be tampered with from the moment it is collected from the source and presented in the report.

Step 4 – Documentation
Everything you do while investigating needs to be documented.
When documenting, you have to think about getting all the necessary evidence written down. You have to explain what it is and its significance, and at the same time, make sure that hash values and time-date stamps are accurate.
Because if there is an inaccuracy, that could present problems in court. The defense could argue it’s not a 100% forensically solid process. They would say that if there is an error in hash value and time-date stamp, it could also be an error in any other evidence.
You can find that that tiny little thing can undermine your whole case.
Saving time to catch criminals instead
When it comes to documentation, one big challenge is time. Since you have to be able to use your investigation as evidence, it needs to be documented in specific ways and in a particular order to hold up in court.
Documentation can also be highly stressful for investigators due to the risk of being cross-examined in court if the job is poorly done.
To use data from your digital investigation as evidence, you must show proof that the file is exactly the way you found it and that no one has altered the evidence.
As we said earlier, this job is time-consuming. Many of today’s investigators do this in Word by writing, copying and pasting, and so on.
Documentation is, therefore, a part where we highly recommend that you have a tool to do all of it automatically. This will save you time to do more important things – like catching criminals.
If you want to know how Paliscope Build can help document your investigation automatically, please contact us for a free trial.
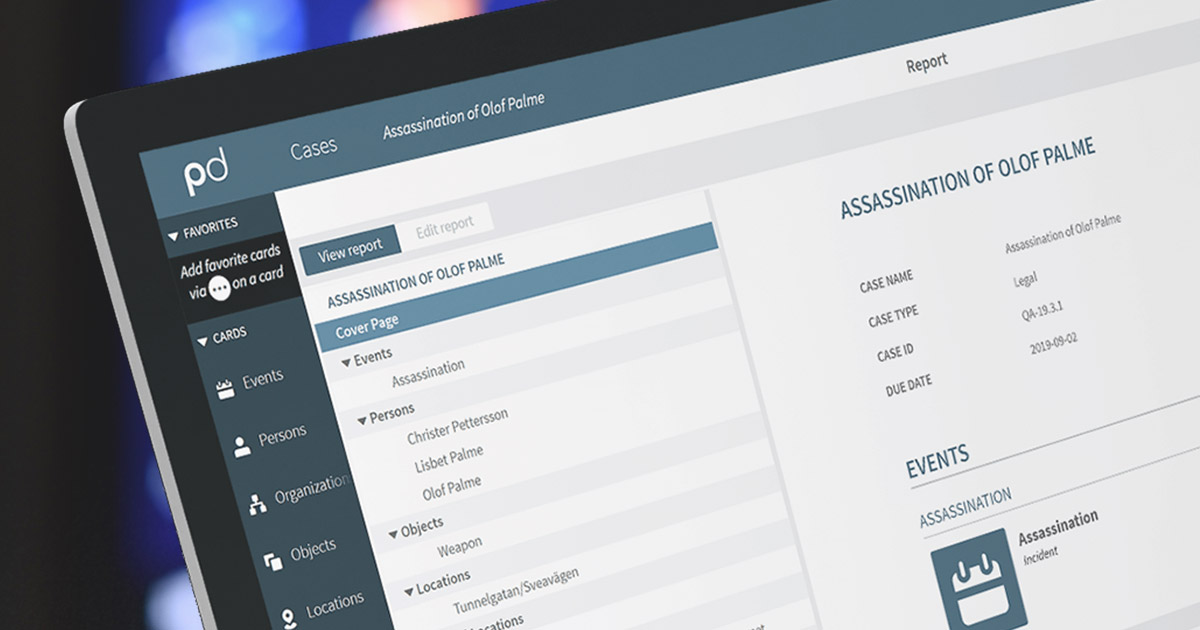
Step 5 – Reporting
Reporting is what you do with all your documentation. In the report, you present all the evidence you have found, and it needs to be presented in a way so that people with no technical background can read it.
We have previously written an article about reporting since it is so essential for the outcome of all your investigative work. In the article, we interviewed Dario Beniamini, who spoke about how the report should be more like storytelling and less technical.
You can read the article here.
A time-consuming job for digital investigators
One of the biggest challenges for digital investigators is the time spent making structured and well-communicated “easy-to-read” reports.
Reports are, among other things, used as evidence in court which means that it’s important that the information it contains is accurate, well structured, and easy to use.
No easy quick fix for reporting
We wish we could give you an easy quick fix to this problem since we know many digital investigators struggle with reporting. But we can’t think of another solution other than using our platform in this case.
Making automated reports is one of the most important tools we have in Build.
When you use Build to collect evidence, the system automatically structures all your data into easy-to-follow reports.
It means time that investigators would normally spend copying, cutting, and structuring data into a document manually can now be directed towards detecting and monitoring other criminals instead.

Step 6 – Expert witness
After you have done your investigation, it is common to be called as an expert witness in court. This means you will be the one who presents all the evidence you have found throughout the investigation.
Being an expert witness can be challenging. The defense will always try to discredit your work and try their best to find ways for the evidence to be thrown out.
A famous example of this is the trial between Johnny Depp and Amber heard, where both sides had expert witnesses, and both sides tried to discredit each other.
Johnny Depp’s expert witness came from a military background and worked for a company that dealt with all sorts of law enforcement and digital forensics cases. But Amber Heard’s team argued against the expert’s credibility by pointing out: “you don´t have a University degree in computer science.”
Amber Heard’s expert witness had a degree in computer science but lacked experience.
So they will find flaws in whatever experience or education you bring to the table. This is why it is so important to come well prepared.
Mock trials
Hopefully, when you study to become a digital forensics investigator, you get to do mock trials as a part of your studies. It gives you some experience and a heads up on what questions they will ask. In addition, you will have time to testify to your experience and back up the process you did during the investigation.
Unfortunately, mock trials are not always a part of the educational process.
The least you need to do to prepare yourself is sit down with the defense team and prosecutor to go through the case and all questions you could get during the trial.
Tools to use for digital forensics investigations
There are many tools out there for digital forensics investigators. The problem is not finding them but choosing which one to use.
We have spoken to Professor John Walker about his favorite tools; you can read all this in the article “Five useful tools for online investigations.”
The tools John is talking about in the article are a mix of tools used for investigation but also to protect yourself from cyber-attacks and educate yourself in Chinese aspects of investigations.
But there are some other tools that are essential for doing digital forensics investigations.
- SingleFile — This tool creates copies of the HTML page you are investigating.
- Hunch.ly — This tool is used to copy webpages (but not forensically, so you still need to hash it)
- Hashgenerator — As the name suggests, this tool generates hash values for your evidence.
- Hash Checker — After hashing, you need to check the hash value.
- Word — Microsoft Word to document and write your report.
These tools are very basic, but they are the ones many investigators use when doing an investigation.
It takes a lot of time to hash, timestamp, document, and report manually, and there is a safety aspect to consider. Doing everything manually puts a lot of responsibility on the investigators. If something is missed or unclear, the evidence could be thrown out when presented in court.
Therefore we recommend our tool Paliscope Build. With Build, you don´t have to worry about hashing and other things because Build does everything for you.
Build automatically puts a hash value and timestamp on all the evidence. And while you are doing the investigations, it automatically documents and generates a report.
Paliscope Build saves you time and is much safer than doing it manually.
If you want to try Build for free, please contact us here.
An important skill for a digital forensics investigator
To be a great digital forensics investigator, you must have technical knowledge. That is the number one skill to make it in the occupation.
Anyone can look through social media, find evidence and use a tool to hash and stamp the evidence automatically — that is not the difficult part of the job.
The tricky part is knowing things like how a file was deleted, how it was able to be recovered, the difference between Exif data and metadata, and how to see if a picture has been altered or not.
How good you are at this will make the difference between being a digital investigator or a great digital investigator.
Being technical is essential when you collect evidence and write your report, and it is also vital for the day you will sit in court as an expert witness.
If you have technical knowledge, you will appear more competent in court, which is key for your evidence to be creditable.
Courses and Certifications
The best way to become a digital forensics investigator is to go down the certification route.
Any course that gives you the CFCE certification will provide you with a job as a digital investigator — but they are expensive.
Cybrary has a library with courses you can study for free, but you pay for the certifications.
Most of the courses are tailored to computer and mobile forensics, but if you are competent in that, you are likely to also be skilled in web forensics.
Legal aspects– Keep updated with GDPR.
Legal considerations vary depending on your organisation and the purpose of the investigation. For example, Law Enforcement must comply with legislation that may not necessarily apply to an insurance company.
Giving a “one fits all solution” to legal challenges is hard. But one thing all organizations acting in the EU have in common is the legal requirement to comply with GDPR.
If you work with digital investigations, it might be hard to know what parts of GDPR are relevant for your work. Therefore, your organization should have an experienced Data Protection Officer (DPO) who can develop and maintain GDPR compliance.
An example of something regulated in GDPR is how long you are allowed to store data. Therefore, it is important to ensure you don’t hold on to data any longer than necessary.
Having a system where you can keep track of important information like this is a good idea since it can be a costly mistake to be found in breach of Data Protection.
So, what systems can you use to comply with GDPR?
An example of a company that is working with GDPR is Aigine. Aigine reads all information from all data sources and uses unique self-learning AI to identify, legally assess and document personal data to ensure accurate privacy compliance and automated governance.
Paliscope Build has some neat features that take this challenge into account. All data collected within Build is stored locally, and it also has a feature that lets you flag data for deletion after a set amount of time. It will remind you when you need to remove data, and when you are finished with the case, you can choose to delete all related files from your computer.
We hope you found this article helpful. If you have any questions, please feel free to contact us.
Get in touch!
Reach out to learn more or discuss how we can help you in your work.





